Understanding SYSMON
For windows, logging is enabled by default, but the log information provided is not enough, it doesn’t not track important events such a process creation, hence the need for Sysmon.
Sysmon is a tool that is included with the sysinternals suite; it provides a lot of telemetry which increases your ability to catch events.
Why Sysmon? Windows has logged enabled by default, but those logs may not be enough to capture critical events such as processes which will be useful in investigations. This is why we install Sysmon on windows clients to help with this.
Sysmon can help monitor:
- Process creations
- File creation
- Network connections and more..
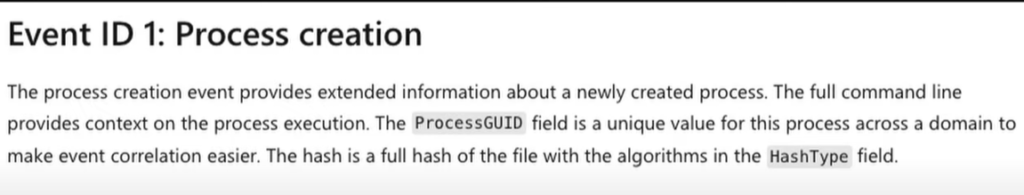
Sysmon also records the hashes for processes which is useful for OSINT (open source intelligence), to present additional context by looking up the file hash.
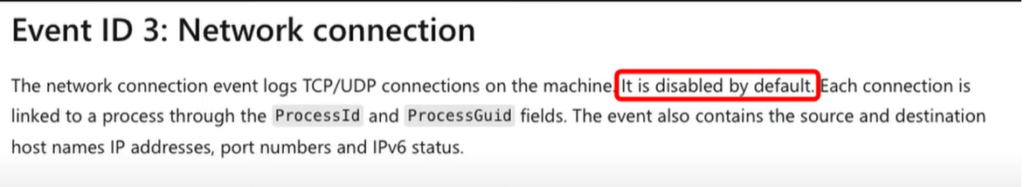
Sysmon can also capture network connections – it id disabled by default, and can be enabled using the Sysmon configuration file.
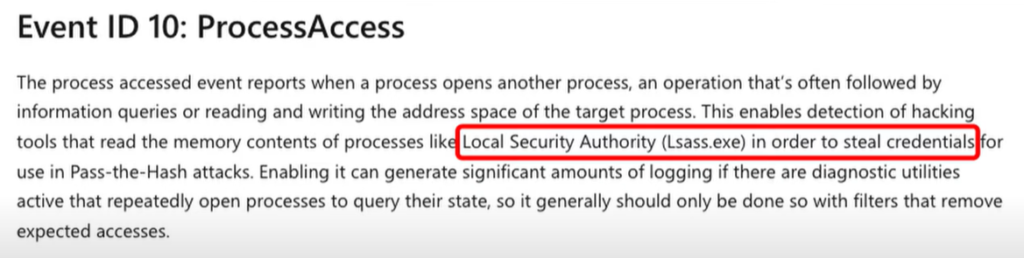
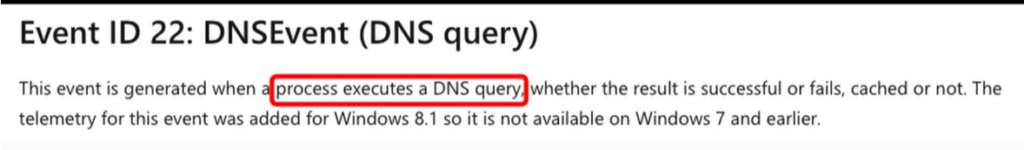
Sysmon (as at this time of writing) has 30 event IDs. Some important event IDs:
System Monitor (Sysmon) is a Windows system service and device driver that, once installed on a system, remains resident across system reboots to monitor and log system activity to the Windows event log. It provides detailed information about process creations, network connections, and changes to file creation time. By collecting the events it generates using Windows Event Collection or SIEM agents and subsequently analyzing them, you can identify malicious or anomalous activity and understand how intruders and malware operate on your network. The service runs as a protected process, thus disallowing a wide range of user mode interactions.
Sysmon Doceumentation:
Sysmon – Sysinternals | Microsoft Learn
Installing Sysmon (On Windows Server)
- Download Sysmon from windows site
- Download Sysmon starter config file from sysmon-modular/sysmonconfig.xml at master · olafhartong/sysmon-modular · GitHub
- Save the xml config file in the same directory as the Sysmon executables
- Run powershell on your windows system as Administrator
- Browse to the Sysmon folder
- Run the sysmon64.exe file ,and point it to the cnfig file using the command:
Sysmon64.exe -i sysmonconfig.xml
Sysmon installed an started:
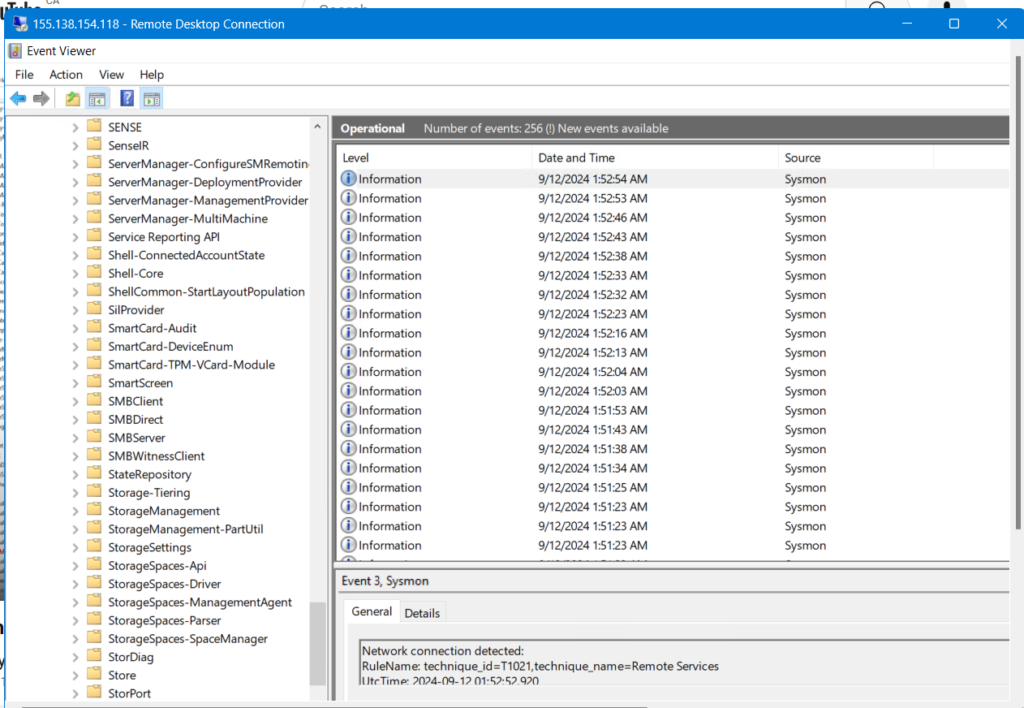
Sysmon will now be a running service and can be viewed in the eventviewer for windows:
Eventviewer > application and service logs > Microsoft > windows > Sysmon > operational
Next, we will start to ingest of log data into Elasticsearch.