Executing malicious executable may trigger other commands to run which gather information about your device or network such as whoami, ipconfig, nslookup, net user etc Such malware can persist in your device through service creation or scheduled tasks. They may also establish command and Control (known as C2 of C and C).
What is C2?
Techniques that adversaries may use to communicate with systems under their controls, within their victims network. (MITRE).Adversaries commonly attempt to mimic normal, expected traffic to avoid detection . Command and Control, Tactic TA0011 – Enterprise | MITRE ATT&CK®
Why is C2 important
For the attacker to be able to perform additional actions to take them closer to their objectives such as credential access, lateral movement, ex-filtration, execute ransomware
What are C2 tools and Frameworks
– Metasploit
– Cobalt Strike
– Sliver
– Mythic
What is Mythic and how does it work?
C2 framework.. allows you to trac payloads and c2 profiles (uses it for agents to communicate bacl to the mythic server)
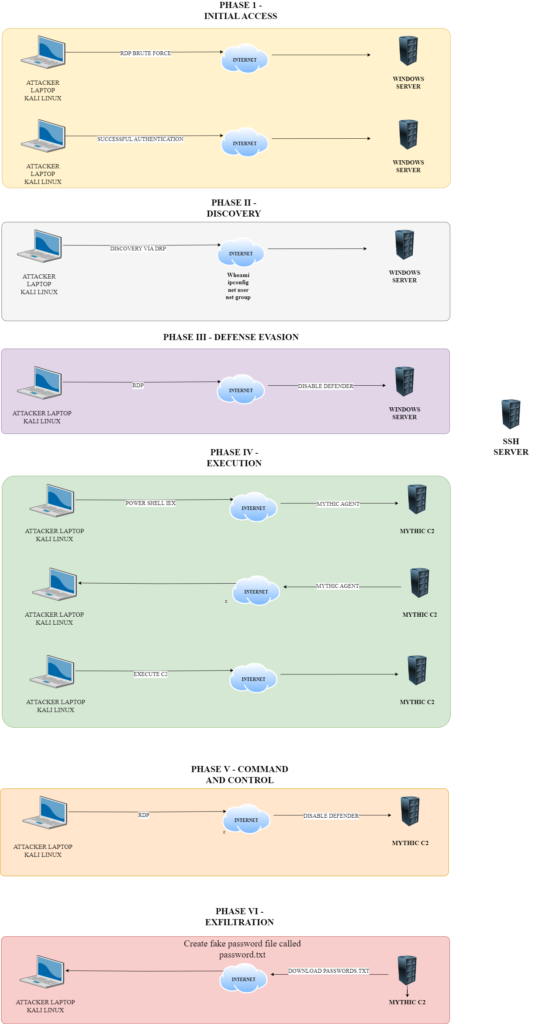
Creating an Attack Diagram.
Create an attack diagram to simulate our brute force attack, access, command and control attack and data ex-filtration operation.