Setup a Kali Linux on your local system (Not cloud). This will be our attack machine for the Command and Control Operation. Mythic server requires a minimum of 2 vCPUs […]
Next, we Setup a new Linux SSH Server as a Test machine for monitoring Brute Force attacks: SSH into the server and update your linux:> apt-get update && apt-get upgrade […]
We deploy a windows server as we did our Ubuntu server earlier. The difference is that this will not be in in VPC network, as defined in our Network diagram […]
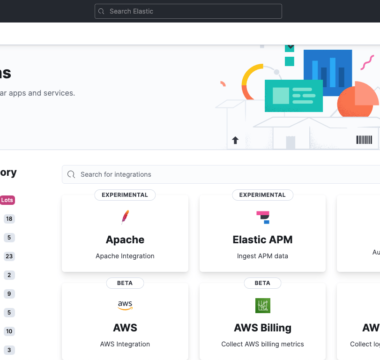
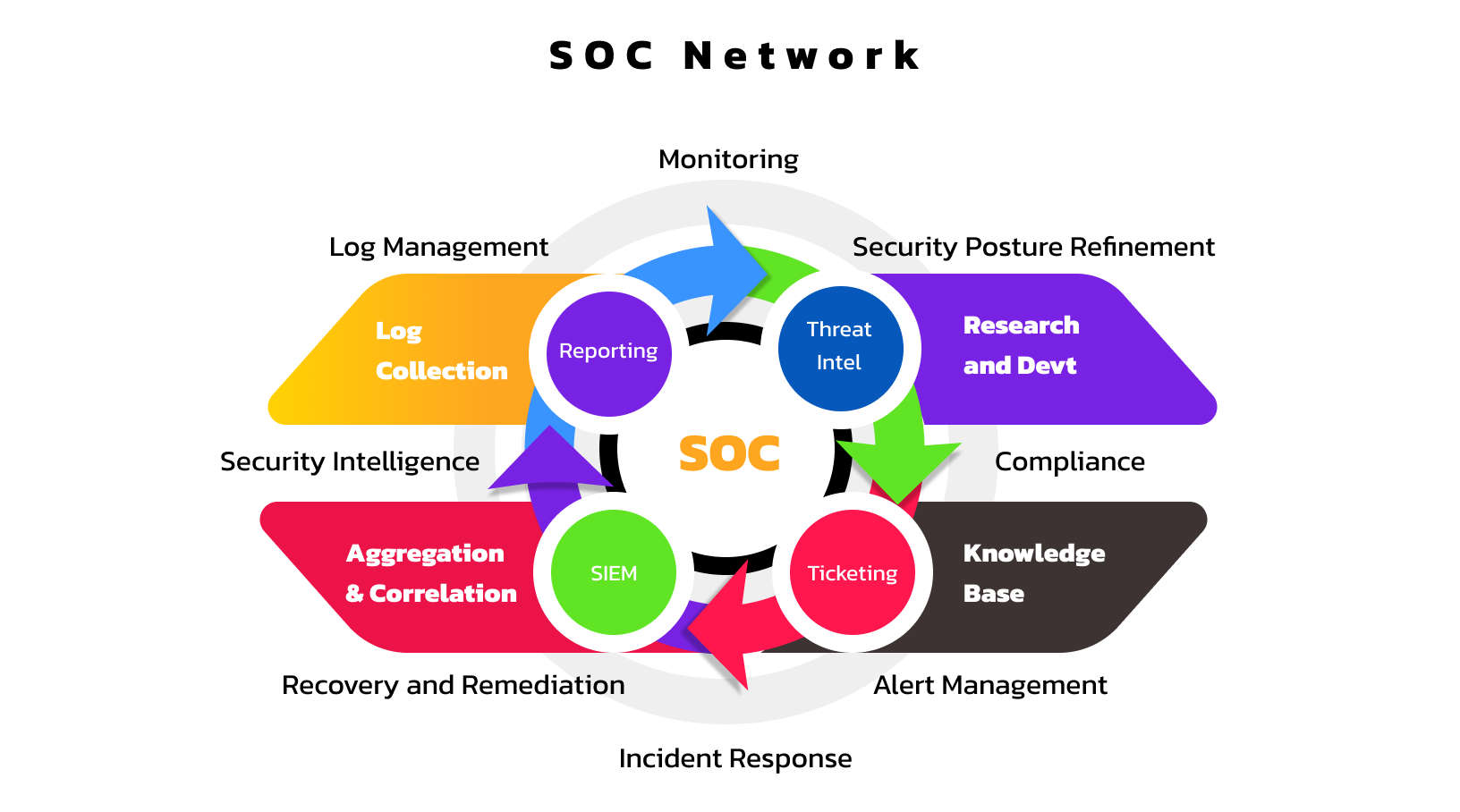
This challenge in aimed at gaining SOC (Security Operations Centre) analysis skills. I will be exploring different aspects of SOC operations and analysis –setting up the ELK (Elasticsearch, Logstash and […]