Investigating the things to look for in a brute force attack Go to ES > Security > alerts We look to investigate the following when we investigate an Alert and […]
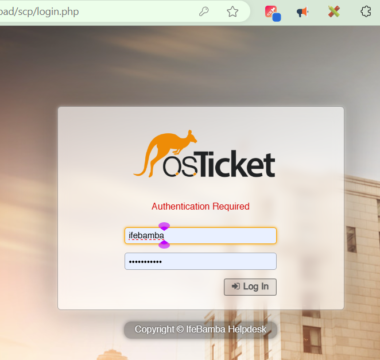
Helps keep track of the task at hand, provide an audit trail and accountability. From a SOC perspective, a ticketing system is essential in fulfilling the AAA triad (AAA Framework) […]
Investigating our recent mythic activity, we return to ES > Discover. Here we search for “svchost-ifebamba.exe” which is our payload, we get some log information below: – we can see […]
Elasticsearch > Analytics > Maps … the you can compose your query: event.code: 4625 and agent.name: IfeBamba-WINSERVER Add Layer > Select Choropeth: Use the Add layer options as seen in […]
Next, we Setup a new Linux SSH Server as a Test machine for monitoring Brute Force attacks: SSH into the server and update your linux:> apt-get update && apt-get upgrade […]
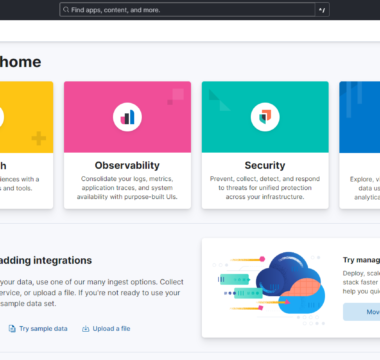
Elasticsearch Ingest Data Ingesting Sysmon and Windows Defender logs into Elasticsearch Click on Add integrations Search “Windows” and you get We click on Custom Windows Event logs, to gather logs […]