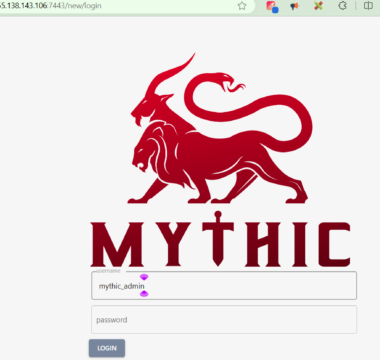
Setup a Kali Linux on your local system (Not cloud). This will be our attack machine for the Command and Control Operation. Mythic server requires a minimum of 2 vCPUs […]
Executing malicious executable may trigger other commands to run which gather information about your device or network such as whoami, ipconfig, nslookup, net user etc Such malware can persist in […]