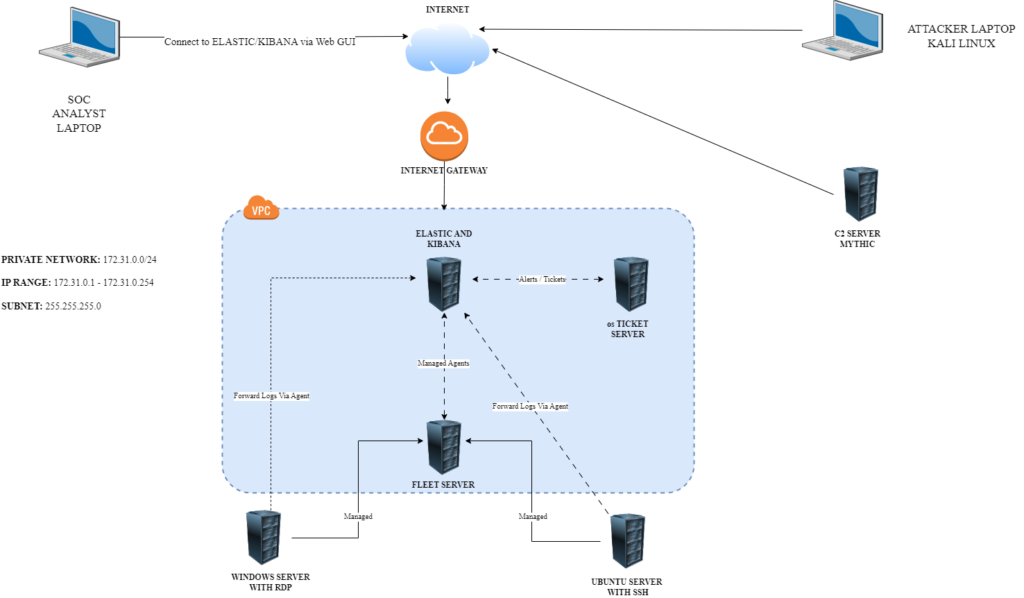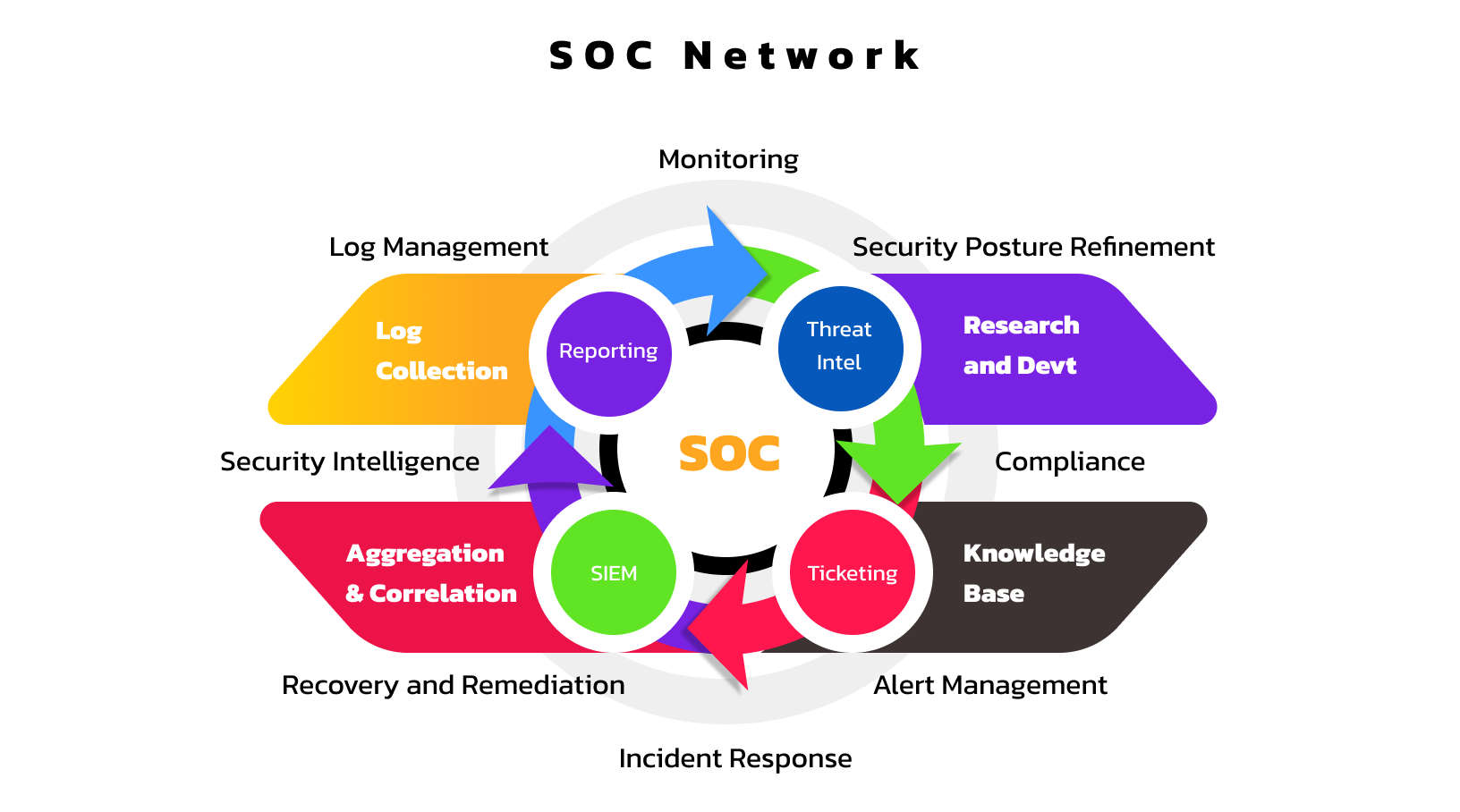
This challenge in aimed at gaining SOC (Security Operations Centre) analysis skills. I will be exploring different aspects of SOC operations and analysis –setting up the ELK (Elasticsearch, Logstash and Kibana) stack, configuring our monitoring environment with Ubuntu Linux and Windows Server, installing and configuring agents and policies, simulating SSH and RDP brute force attacks, exploring C2 (command and control) attacks and malware deployment with Mythic Framework, integrating our ELK stack with a ticketing system (osTicket), investigating and correlating logs, malware detection, designing dashboards with Kibana, and deploying Elastic’s EDR (Endpoint Detection and Response) with Elastic Defend.
I will be deploying this Lab in the cloud using Vultr.
This Challenge is based on the 30-day SOC analyst challange by Steven Rocks on his MyDFIR youtube page where he offers practical tutorials in Cybersecurity, and in particular Digital forensics and incident response (DFIR).
Objectives:
– Design a Logical Diagram of our environment and infrastructure for this Lab
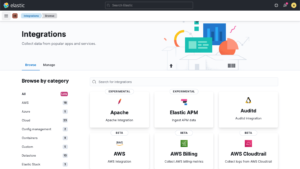
– Introduction to the ELK stack
– Elasticsearch setup and installation
– Kibana setup and installation
– Installing our Windows Server 2022 component
– Elastic Agent and Fleet server Introduction
– Elastic Agent and Fleet server setup
– Understanding Sysmon for Windows Telemetry
– Setting up Sysmon
– Ingest Data with Elasticsearch
– Understanding Brute force attacks
– Installing Ubuntu Server 24.02
– Installing Elastic Agent on Ubuntu Server
– Creating Alerts and Dashboards in Kibana
– RDP
– Creating Alerts and Dashboards in Kibana 2
– Understanding Command and Control (C2)
– Creating our Attack simulation diagram
– Mythic Server Setup (Mythic Framework)
– Mythic Agent setup
– Creating Alerts and Dashboards in Kibana 3
– Ticketing Systems
– Installing an OSS ticketing system with osTicket
– Integrating a Ticketing System (osTicket) and ELK
– Investigating SSH brute force attacks
– Investigating RDP brute force attacks
– Investigating Mythic Agent attack
– Setting up Elastic EDR solution – Elastic Defend
Network Diagram: