Investigating the things to look for in a brute force attack
Go to ES > Security > alerts
We look to investigate the following when we investigate an Alert and check its details:
(1) – IP : is this IP known to perform brute force activity?
(2) – Any other users affected by this IP?
(3) – Were any of them successful?
(4) – If so, what activity occurred after the successful login?
(1.) Is this IP known to perform brute force activity?
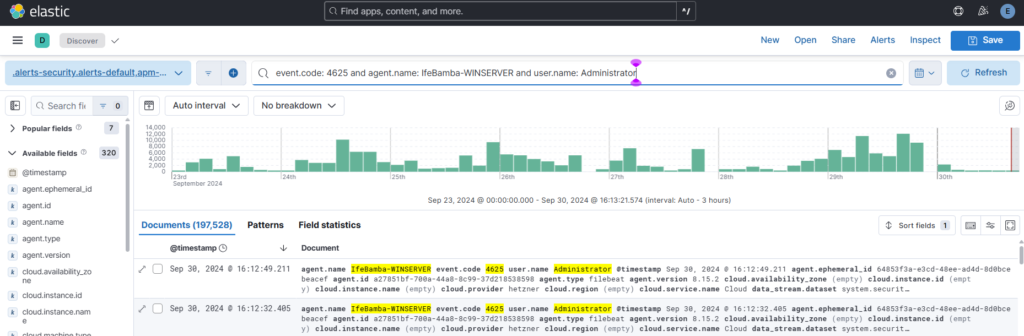
Recall that we successfully brute forced our Windows Server a while back with a Kali attack machine, we can use ES to search for those events:
Unsuccessful login events query: event.code: 4625 and “kali”

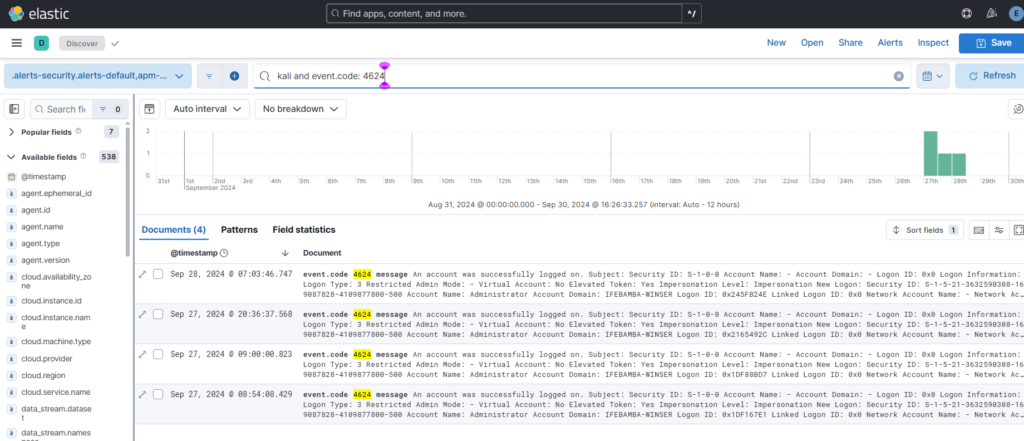
Successful login events query: event.code : 4624 and “kali”
If we investigate further, we can get more details such as IP address
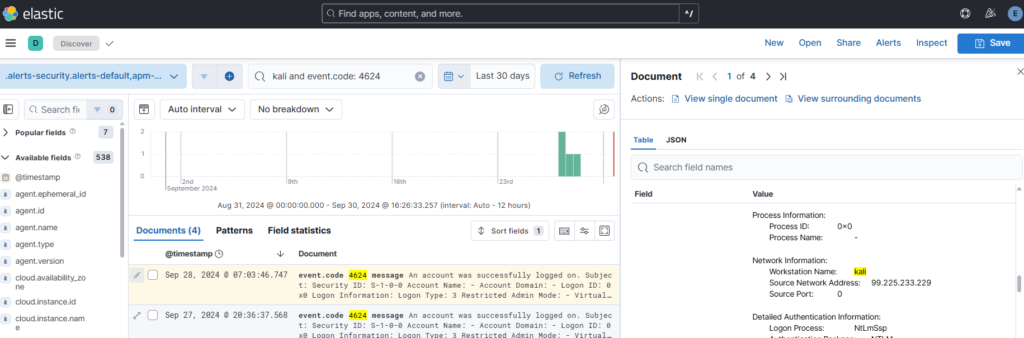
We see the IP: 99.225.233.229
IP Address :99.225.233.229, on ifeBamba-WINSERVER:
(1) – IP : is this IP known to perform brute force activity?
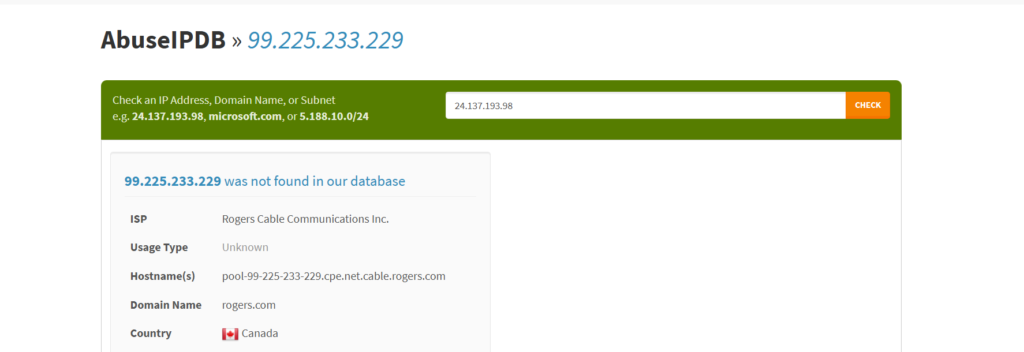
Answer: No
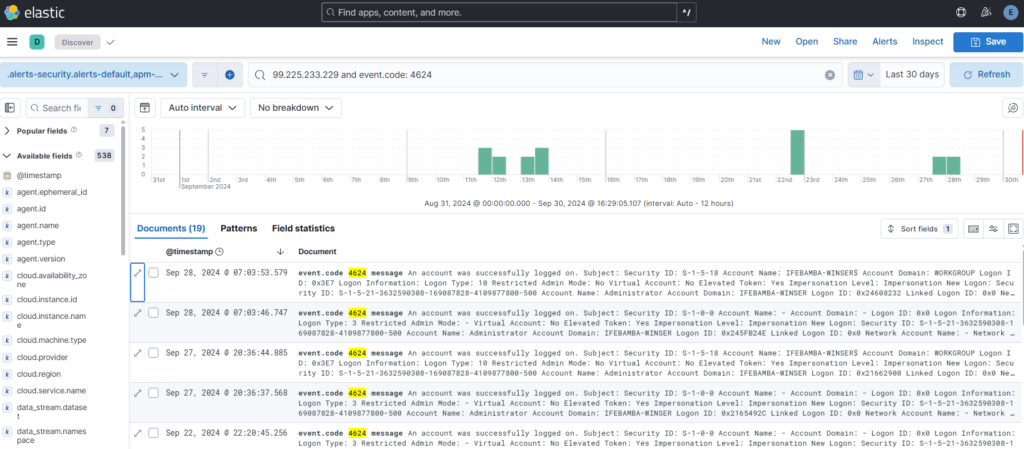
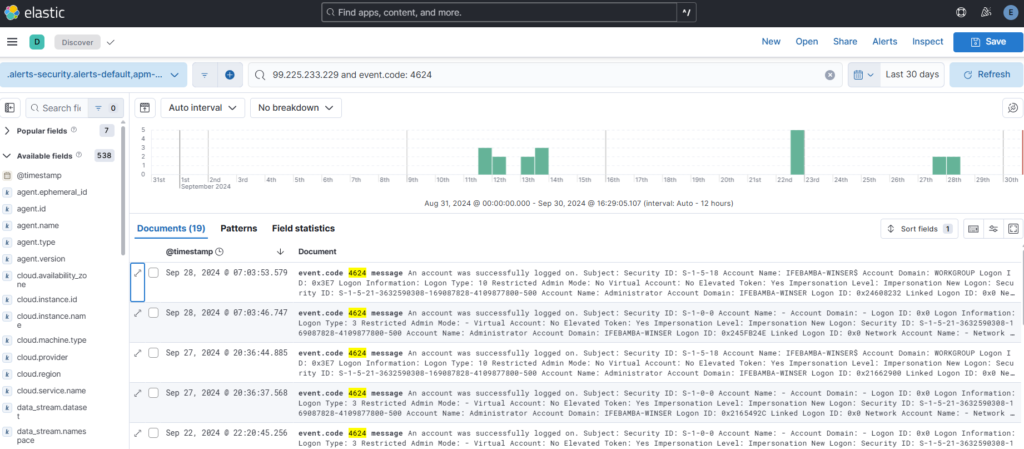
(2) – Any other users affected by this IP?
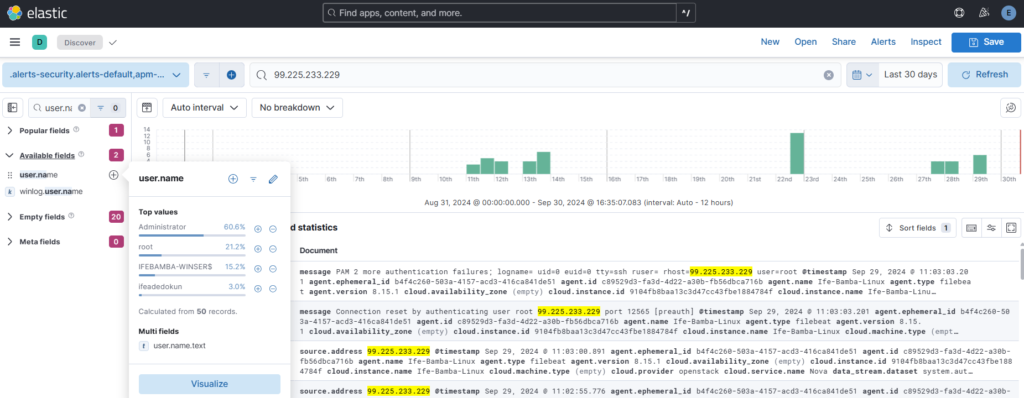
We can see from the scrnnshot above that the accounts: Administrator, root, ifeadedokun were used
Answer: Yes
(3) – Were any of them successful?
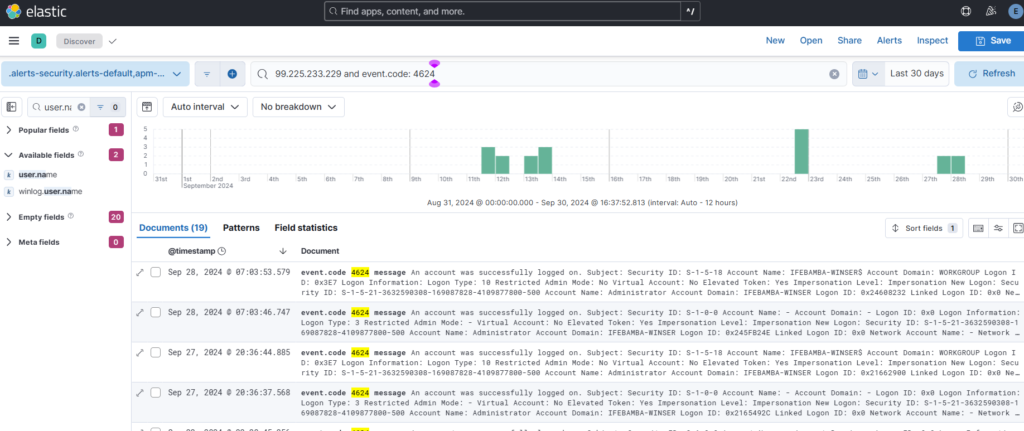
From the screenshot, we see we have 19 successful logins by this IP address.
Answer: Yes
(4) – If so, what activity occurred after the successful login?
Here, we need to investigate the first time the account login was successful, e.g: Sep 11, 2024 @ 21:28:48 , the location of the login, the source domain, when the account logged out and several other investigation by using the log details provided in our logstash.