In this post, I will be conducting an SOC analysis / investigation on an alert generated on a SIEM (Using letsdefend.io) to determine if a suspicious attachment in an email sent to a user in our organization is malicious or not.
I will be running through the steps from alert generation, to case creation, to investigation and analysis and eventual closure.
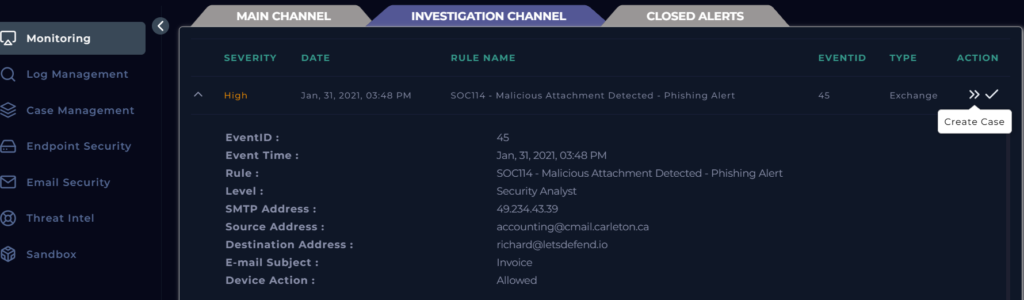
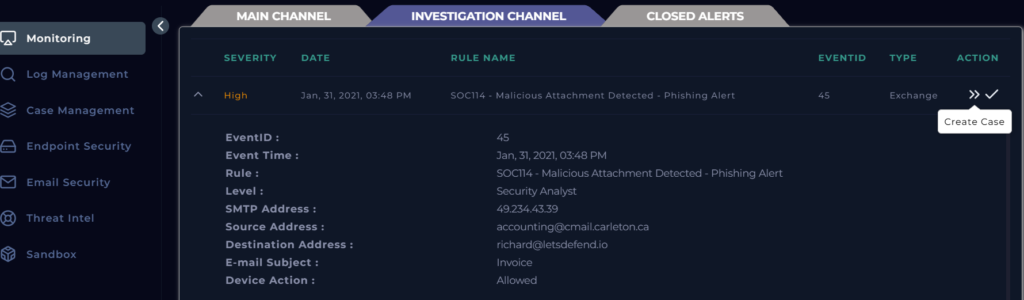
SIEM Alert
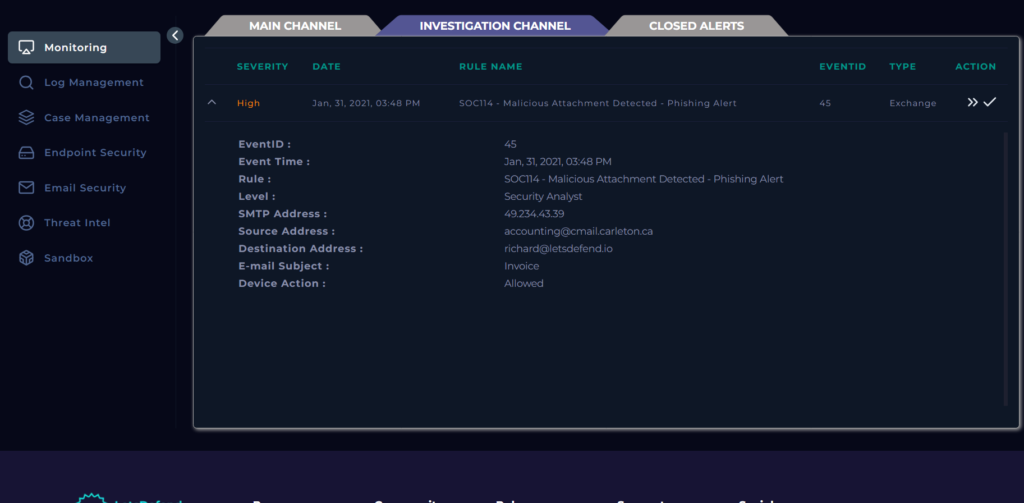
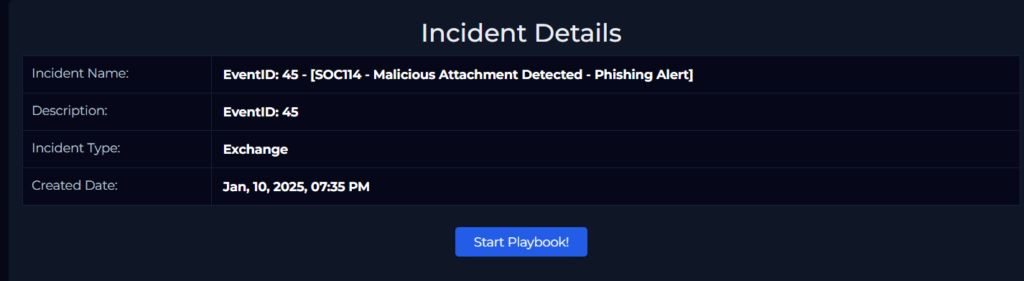
Next, within the SIEM, we create a case so that this alert can be investigated properly by the SOC Analyst.
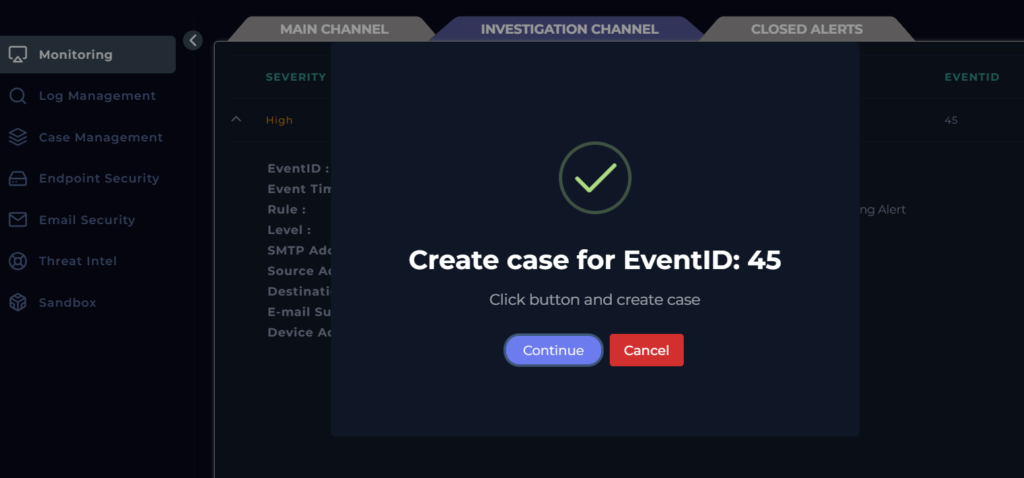
Next, we run the playbook attached to this category of incident for easy investigation
Investigation Details required:
To investigate this alert, we take note of basic alert details generated from the SIEM and other details such as:
When was it sent (Event Time)?
What is the email’s SMTP address?
What is the sender address?
What is the recipient address?
Is the mail content suspicious?
Are there any attachment?
In this case, the SIEM alert supplied us some details such as:
EventID :45
Event Time : Jan, 31, 2021, 03:48 PM
Rule :SOC114 – Malicious Attachment Detected – Phishing Alert
Level : Security Analyst
SMTP Address :49.234.43.39
Source Address : accounting@cmail.carleton.ca
Destination Address : richard@letsdefend.io
E-mail Subject : Invoice
Device Action : Allowed
Email Investigation:
We can investigate the email by searching the source email address and answering a few questions such as if it contains a suspicious link or attachment. Here, we can see a suspicious attachment which we need to further investigate.
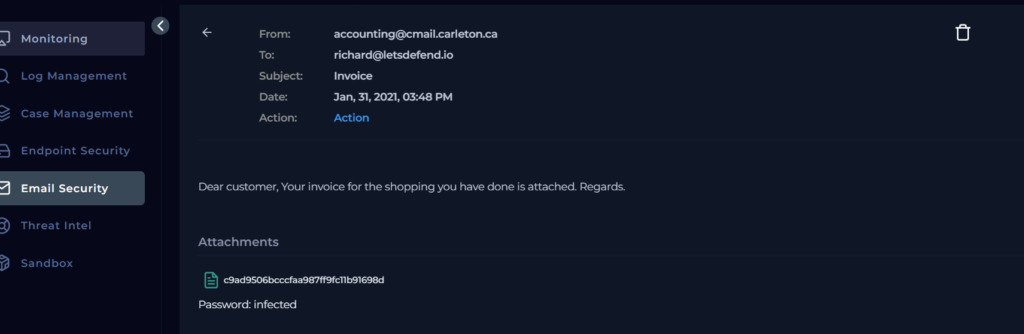
Attachment (Malware) investigation and Analysis:
First thing to note is that email security solutions typically convert attachments to a hash value to identify and analyze them for potential threats. This helps to create a unique fingerprint for the file so that analysts can easily compare ti to known malicious files in a database.
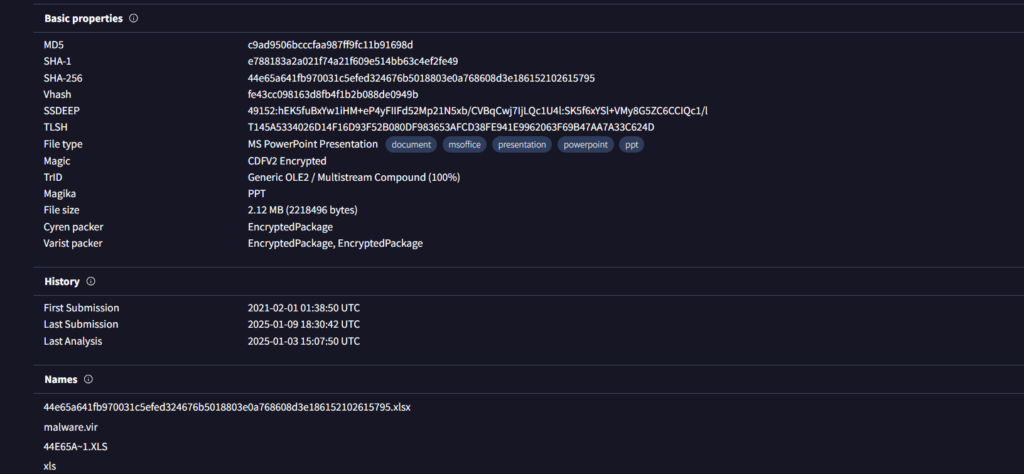
Our hash value for this attachment is:
c9ad9506bcccfaa987ff9fc11b91698d
We can use third party OSINT sandbox tools to investigate our attachment and check for malicious intent. Tools available include, but not limited to:
AnyRun
VirusTotal
URLHouse
URLScan
HybridAnalysis
We will be using some of these tools below to conduct our investigation of a potential malware
VirusTotal Analysis:
We can see that this file has been flagged as malicious by some security vendors:

Its a good practice to analyze your malicious link/file with multiple platforms to be vey certain of your investigation. Lets try Hybrid Analysis.
Hybrid Analysis:
This platform allows us to select a sandbox environment:
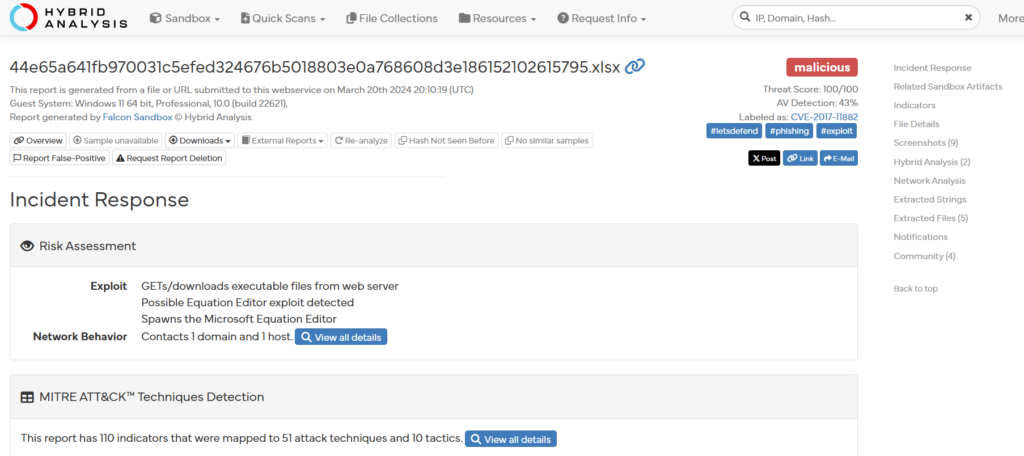
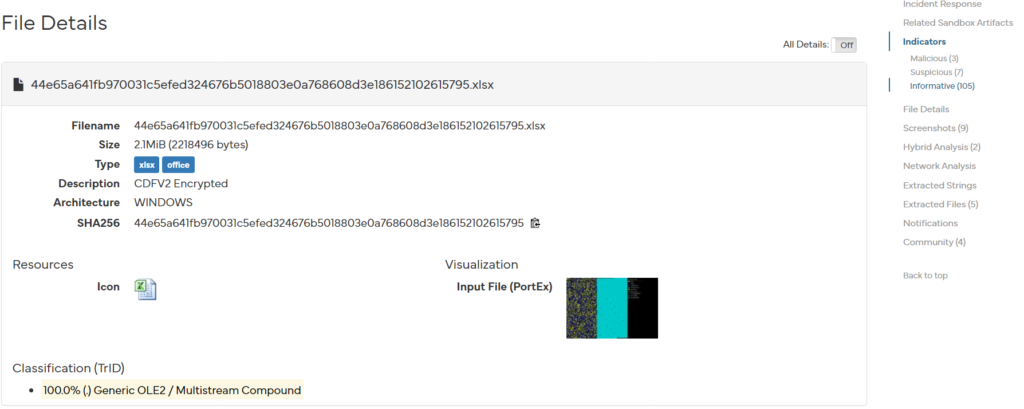
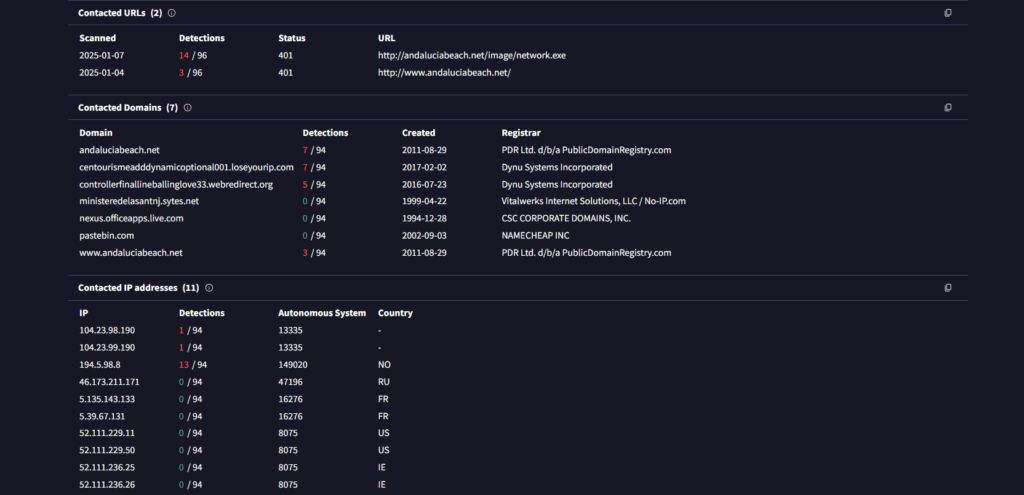
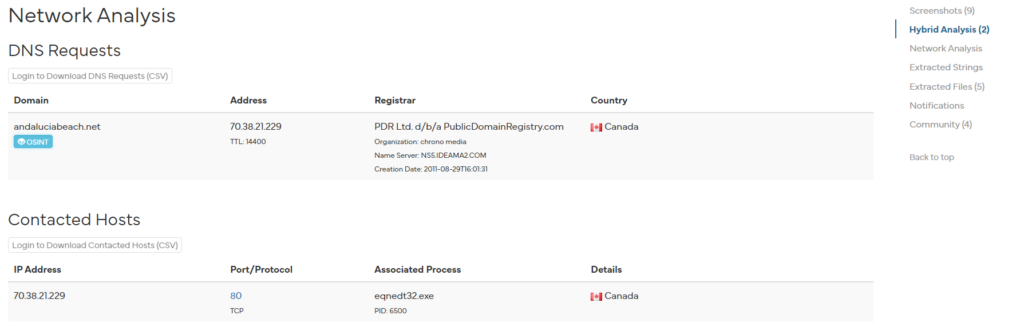
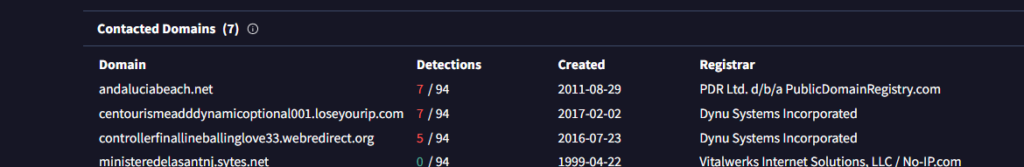
We are presented some Network Analysis scan results for the hash we submitted:
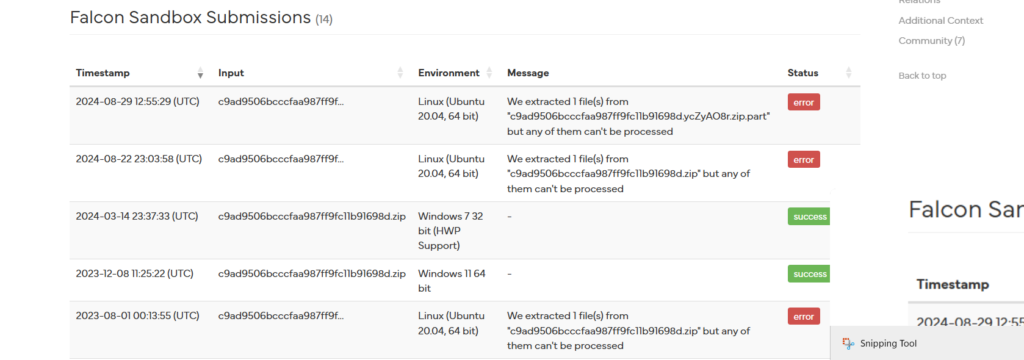
Based on the analysis results from both OSINT platforms above, we can conclude that there was a malicious file attached in the email sent to our internal user.
Next we need to find out what the device action on this Malicious email was; was it allowed, was it blocked? This we can find out in the alert generated by our SIEM initially:
Here, we see device action is: Allowed which means that this Malicious Email got through to the device, and May/May not have infected the computer or breached the user account, if it has been opened by the user.
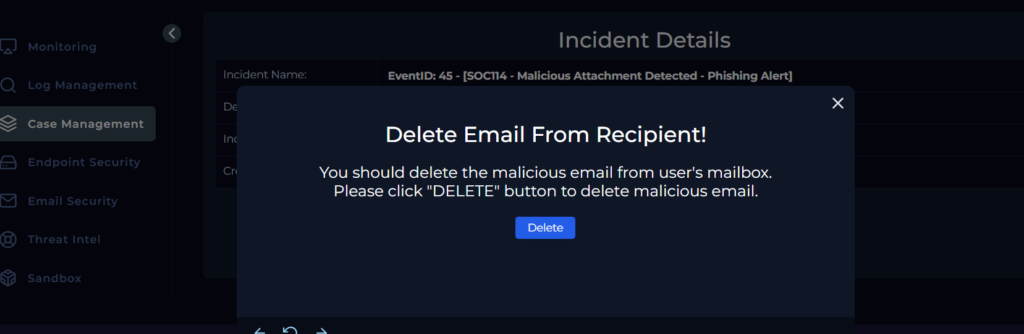
We have to delete the email from the user account:
Further Investigating with AnyRun:
We can see that the attachment in the email is actually a malicious excel document
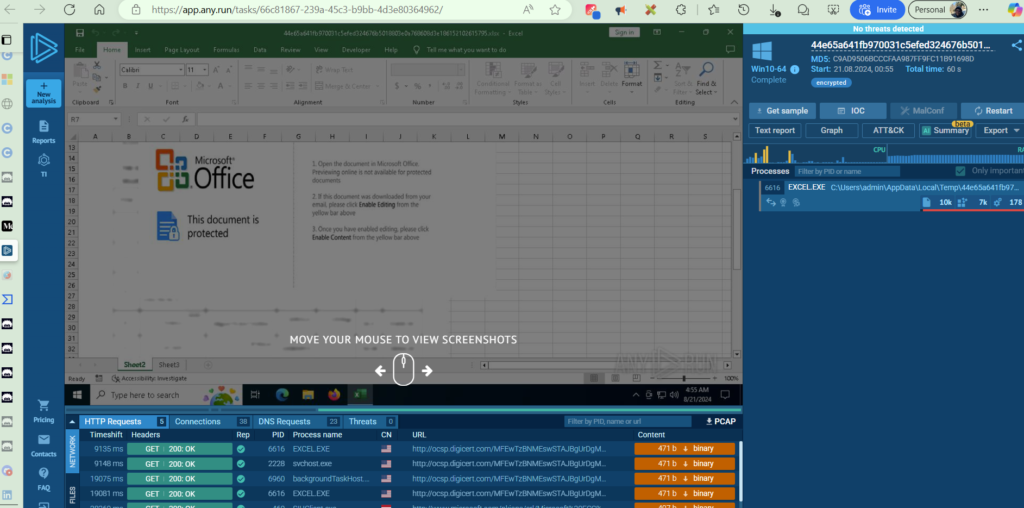
The Malware reports showing the indicators of compromise (IOCs) for this particular file are available on these links: AnyRun, HybridAnalysis, VirusTotal.
We would also like to know if this file was opened by the user, we can know this by the details of our analysis of the malicious Hash.
During the investigation, we were able to get details such as the HASH value of the file, the IP address of the file, etc. This is important because malicious files when opened will usually link up to a c2 (command and control server somewhere on the internet):
Via AnyRun, we see this, note the domain specified:
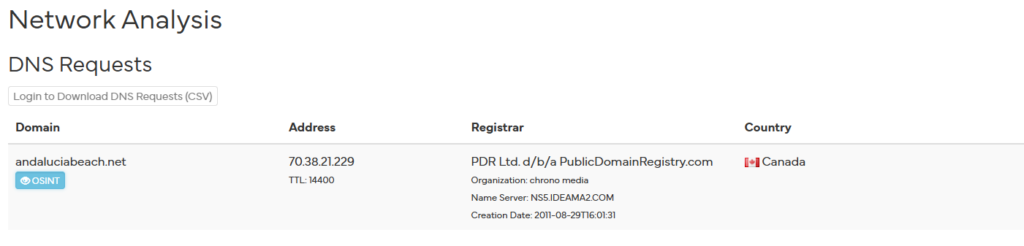
Via VirusTotal we see a contact initiated to the same domain (andalucia…):
We search through our SIEM logs to see if we have any traffic request to the IOC of interest (andalucia.net domain)
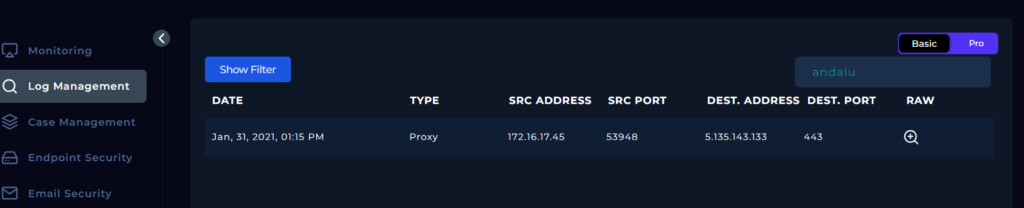
From above, we see that there has been a connection to that IP address so far:
from internal IP address: 172.16.17.45.
To external address: 5.135.143.133
port: 443
Time: Jan 31, 2021 at 1:15pm
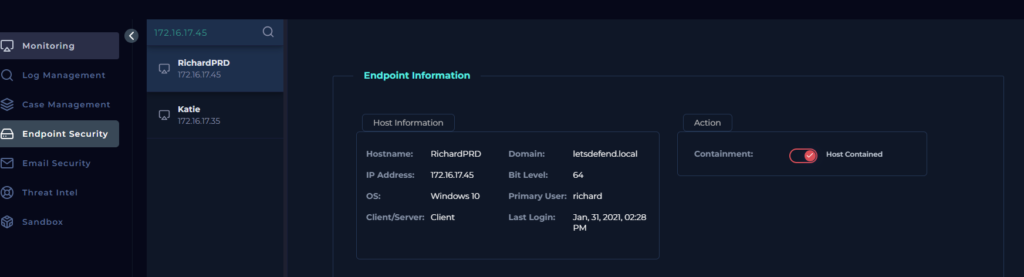
We investigate further by identifying the Internal device with Endpoint Security:
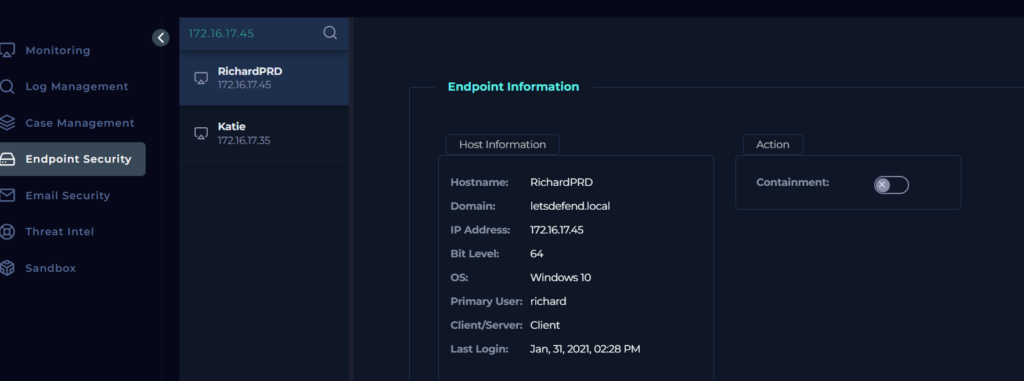
We see that Richard’s machine accessed this C2 (andalucia.net) address, after being triggered by the malware excel document that he downloaded and executed on his device.
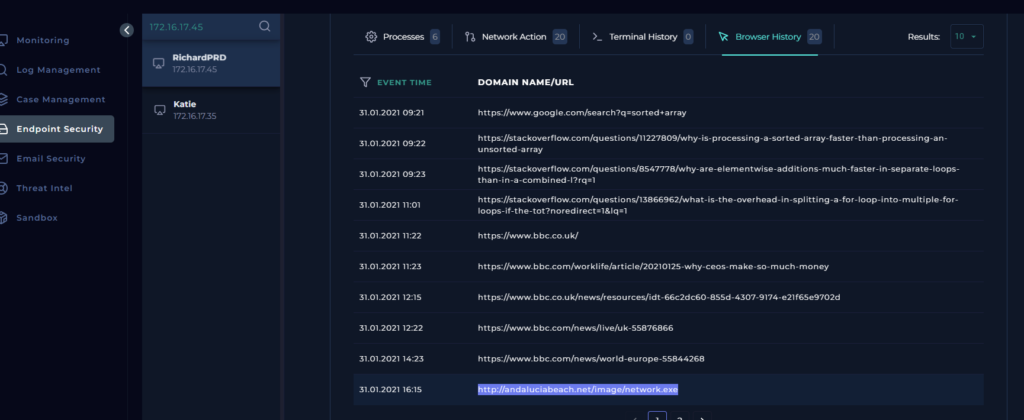
On further investigation, we see that from the browser history of Richard’s endpoint, it accessed the malicious URL as stated above.
Containment
Once this intrusion has been verified, we need to contain he device in question:
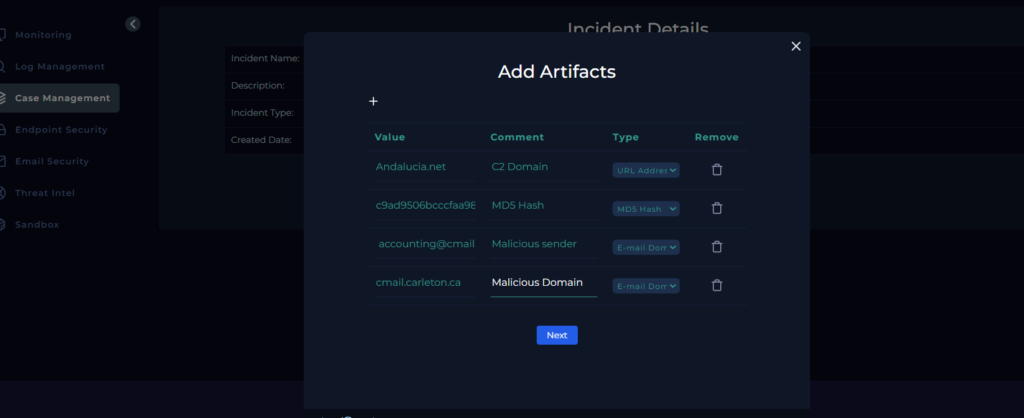
Next we can add artifacts to our case file for further referencing in the future or for newer investigations of malware. Artifacts are Indicator of compromise that the attacker has left behind that we can use for proof of intrusion.
We add the file URL and HASH value:
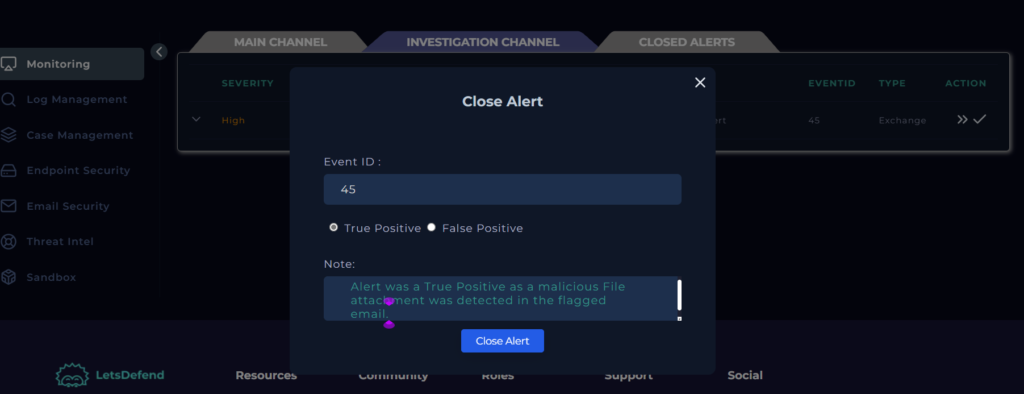
It is also good practice to add comments of your analysis to your casefile to show any reviewer the steps taken for you to come to your conclusion. We also get to tag the Alert as a True Positive, since the investigation showed that the SIEM correctly alerted us to a potential malicious email attachment
Finally, we can close the Alert
In conclusion, we were able to answer the following question posed initially at the beginning of the investigation:
When was it sent? Jan, 31, 2021, 03:48 PM
What is the email’s SMTP address? 49.234.43.39
What is the sender address? accounting@cmail.carleton.ca
What is the recipient address? richard@letsdefend.io
Is the mail content suspicious? Yes
Are there any attachment? Yes
Was Email delivered to the User? Yes
Was the attachment malware? Yes
Was the malware opened? Yes
Did malware attempt to make eternal network connections / reach out to C2 or URL? Yes
Steps Taken: Email was deleted, Device isolated/contained for further actions such as anti-virus scans etc