In investigating a C2 : you will consider the following ways
– Network telemetry (existing C2 sessions have a lot of back and forth telemetry)
– Heartbeat (You can use a tool like RITA)
– Process and Network creations (Using Sysmon – network events use ID 3)
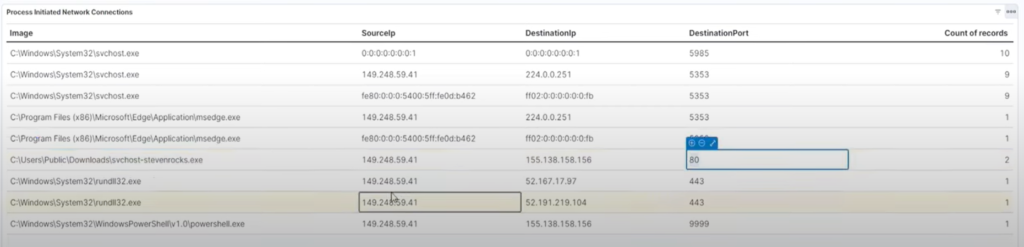
You can create visualizations in forms of tables to collect logs based on certain interesting fields such as destination IP, source IP, destination Port, Image (process name) etc.
For example, a process going out to an external IP address on port 80 could be suspicious
If you use sysmon, always look for your process GUID to correlate your logs to establish a flow of suspicious activity…for every event, record the timestamp and associate it with the activity
Here are some screenshots investigating our c2 payload process (Attack using apollo on Mythic):
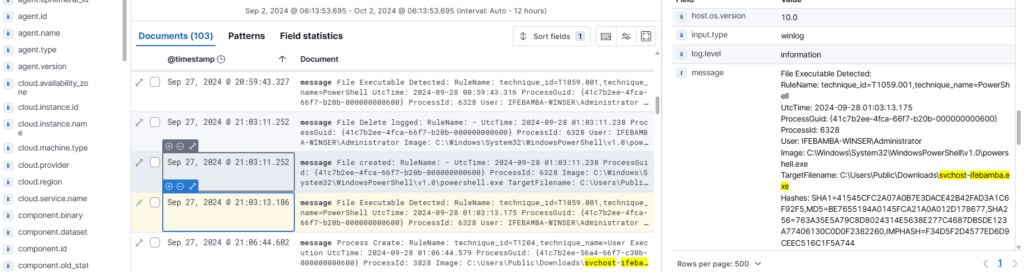
1. File creation detected:
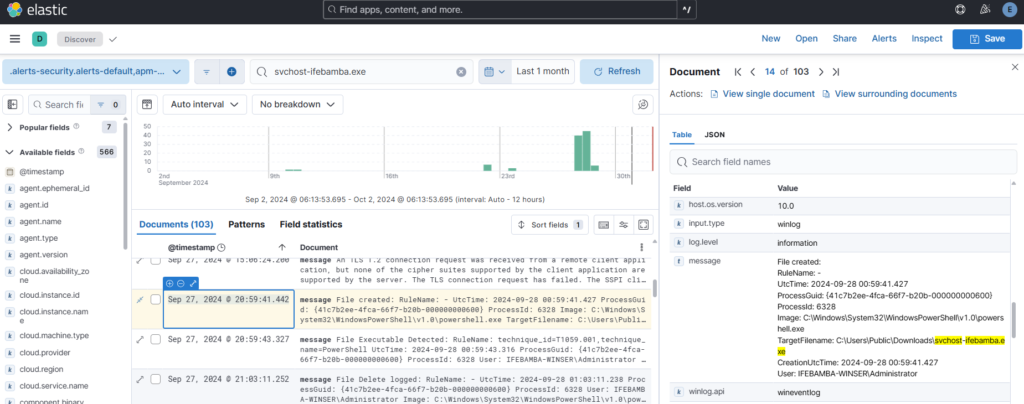
2. File executable detected:
3. process created: note the process GUID: You can copy the GUID and then search
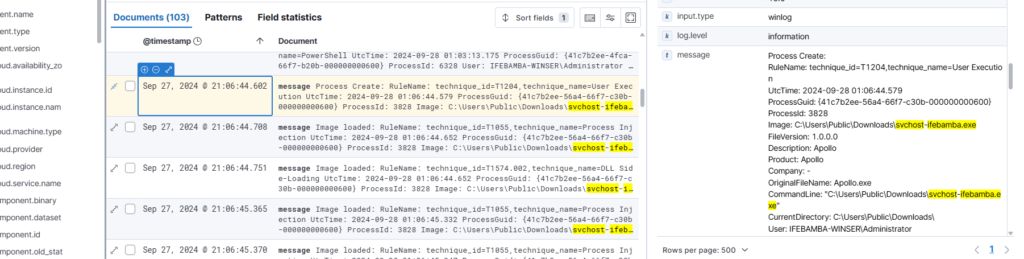
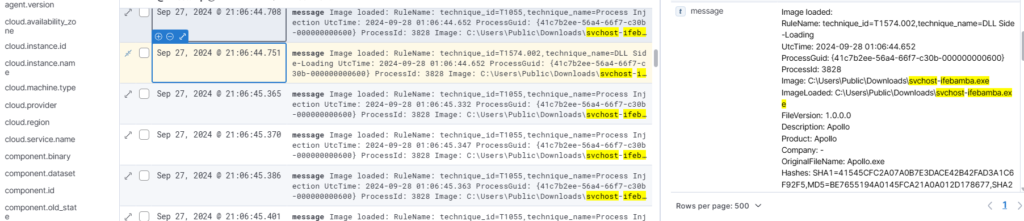
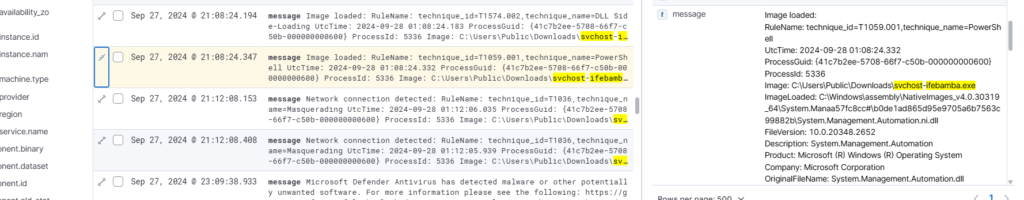
4. Image loaded:
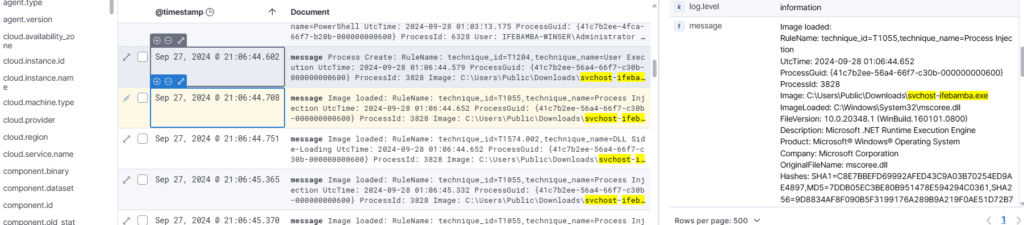
note the rundll technique
note Powershell:
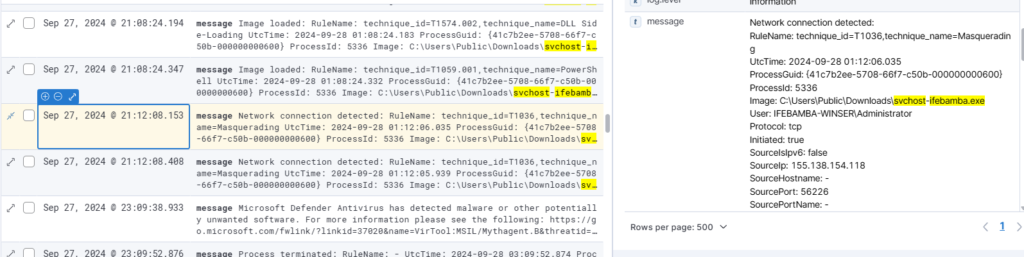
network connection detected: windows server with mythic agent installed reaches out the the mythic server
We enable Windows Defender:
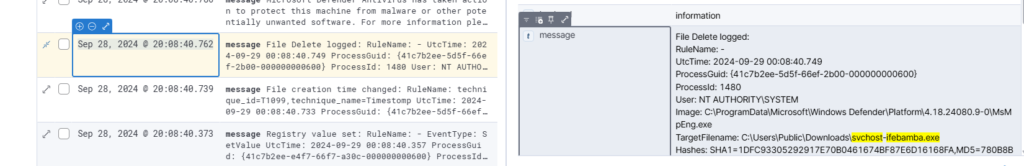
Sep 28, 2024 @ 20:08:40.786 : windows defender detects an attack
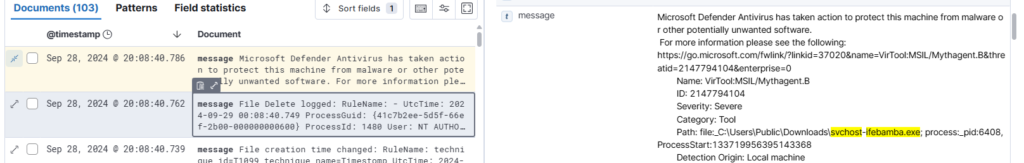
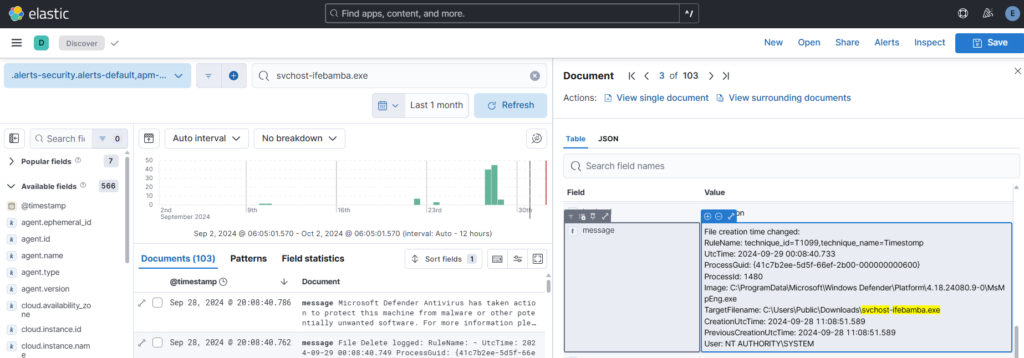
Defender terminates process
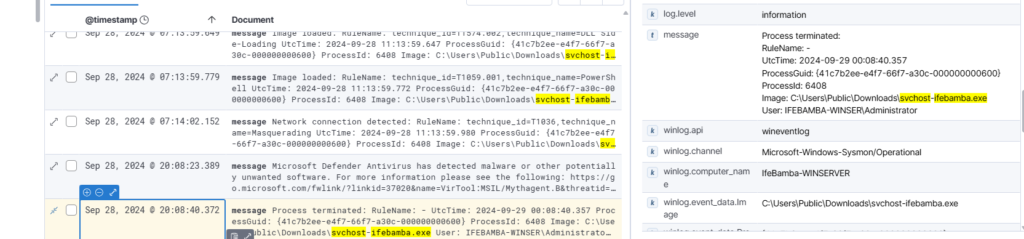
. Sep 28, 2024 @ 20:08:40.762 windows defender deletes the suspicious file: