Elasticsearch Ingest Data
Ingesting Sysmon and Windows Defender logs into Elasticsearch
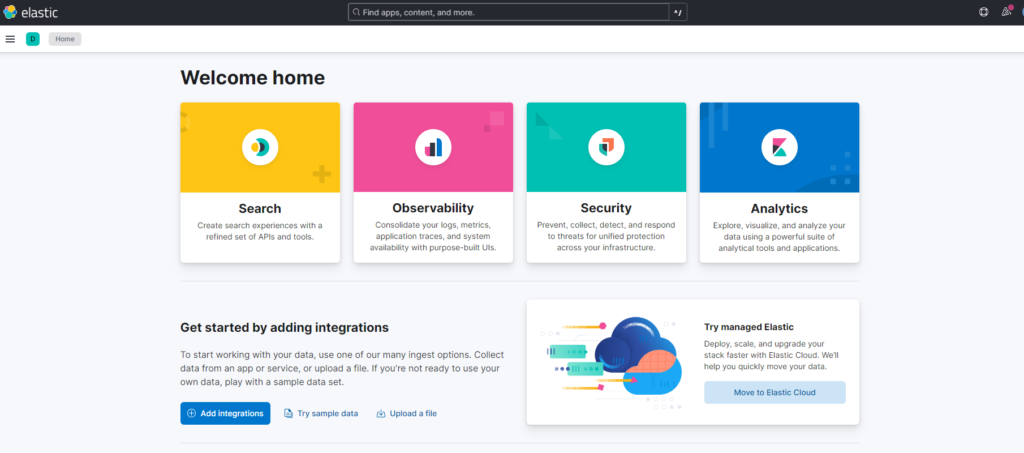
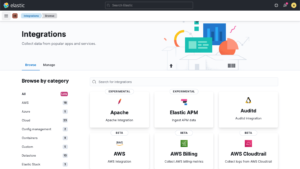
Click on Add integrations
Search “Windows” and you get
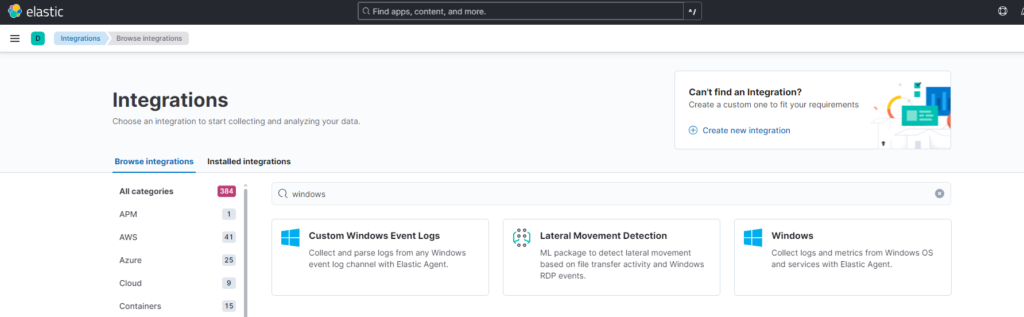
We click on Custom Windows Event logs, to gather logs from Sysmon on windows
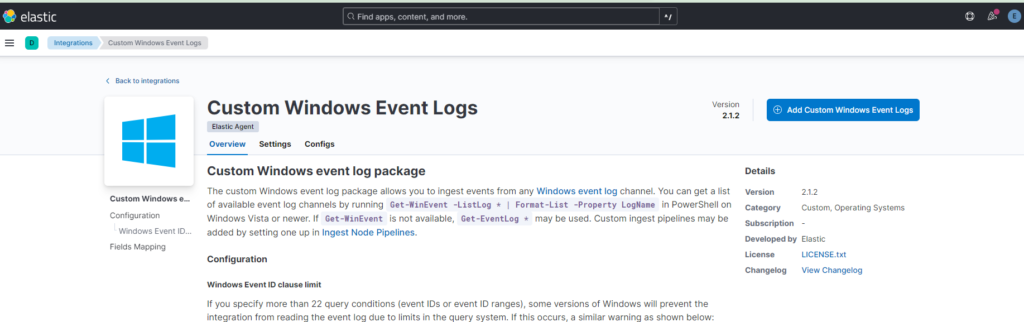
Next, click on “Add custom windows Event Logs”
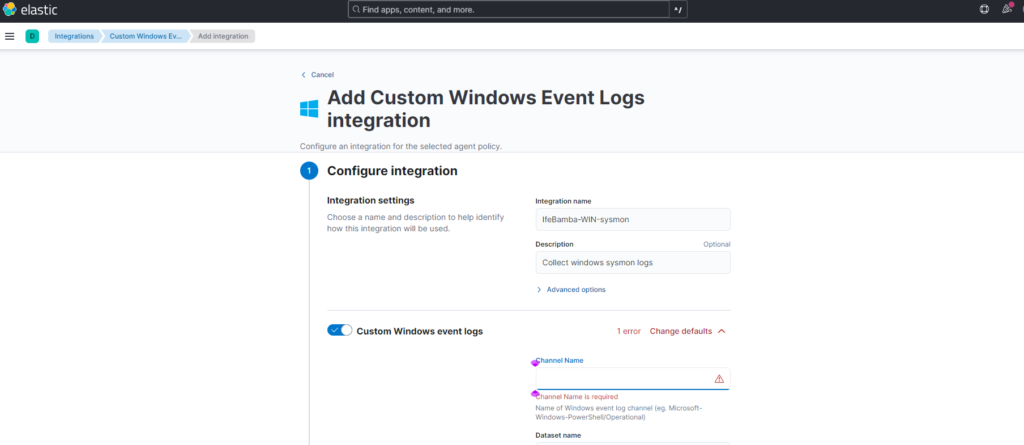
For channel name, we need to go back to our eventviewer in the windows Server.
Eventviewer > application and service logs > Microsoft > windows > Sysmon > operational > right-click > Properties
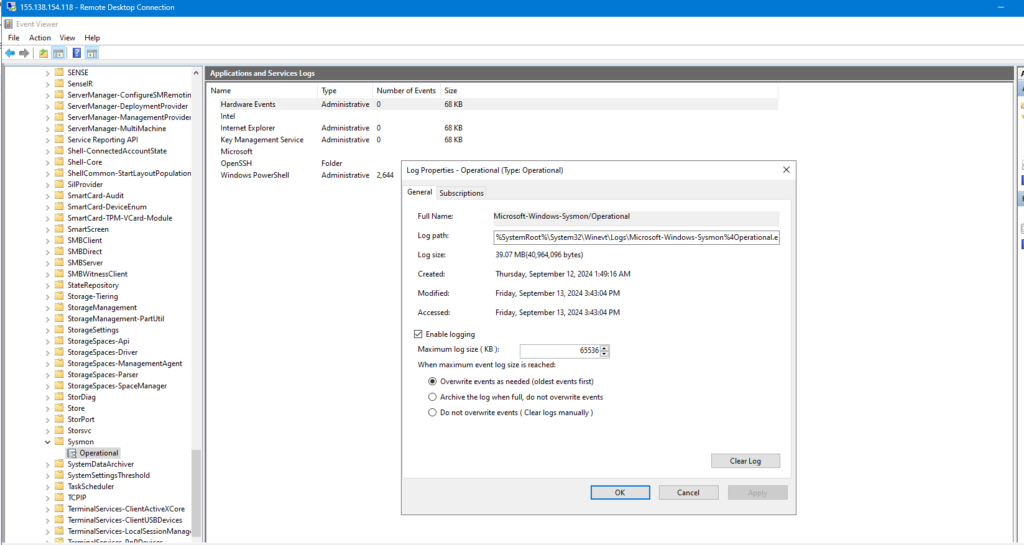
Copy the full name field:
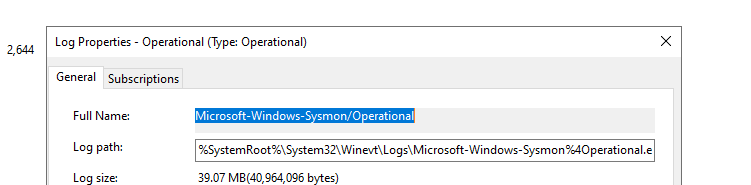
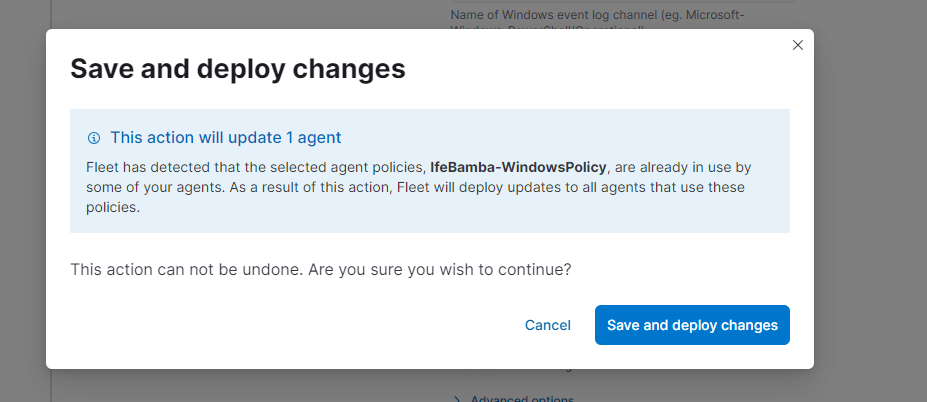
Paste into Elastic Search:
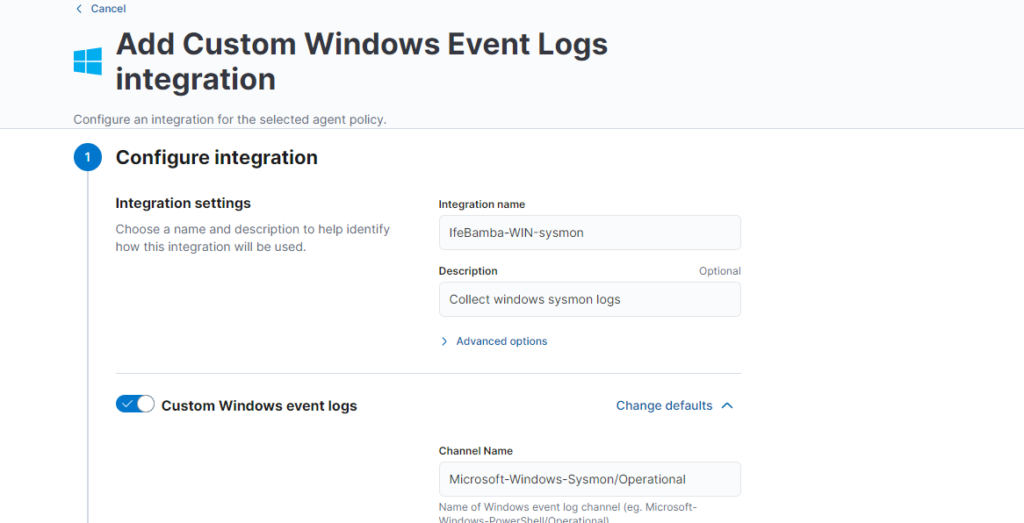
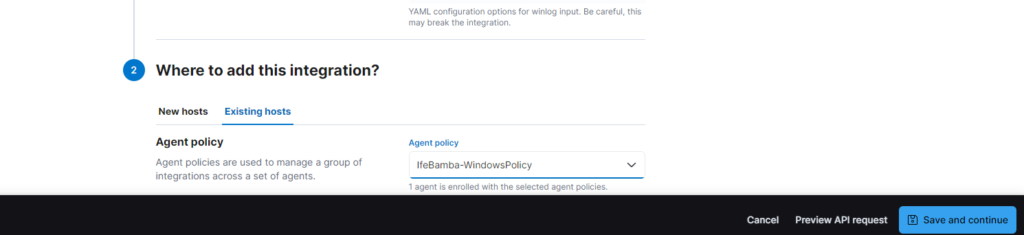
Next, scroll down and add integration to Existing Host; select the agent policy created on the Windows server earlier and Save and Continue

Save and deploy changes:
We repeat the same steps for Windows Defender
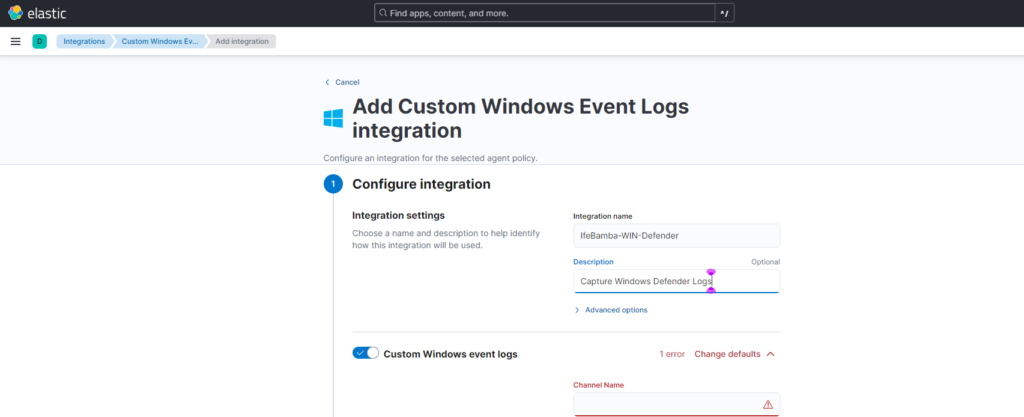
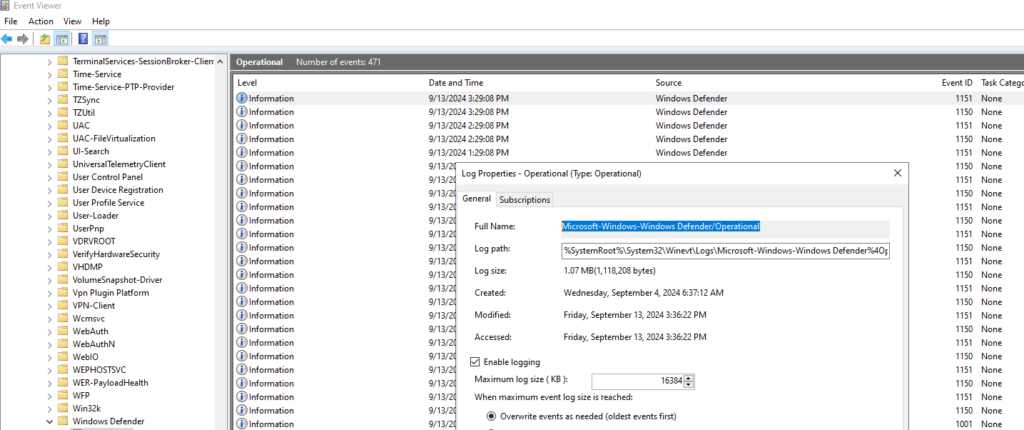
For channel name, we need to go back to our eventviewer in the windows Server.
Eventviewer > application and service logs > Microsoft > windows >Windows Defender > operational > right-click > Properties > copy the Full name
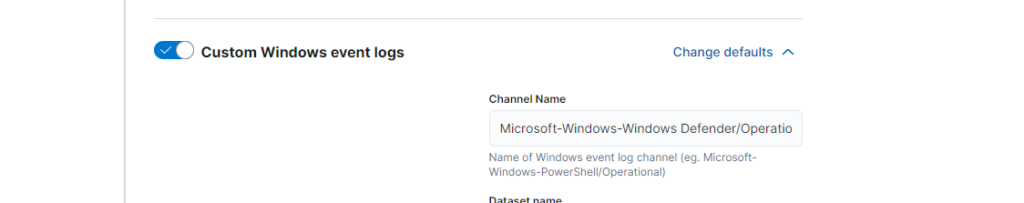
Windows Defender publishes a lot of event logs, especially informational logs which we may not need.
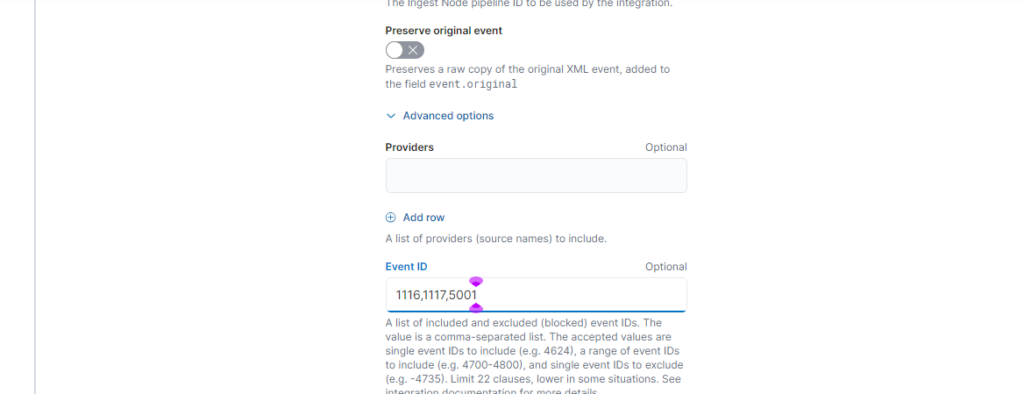
For this lab, we will limit our logs based on Windows Defender event IDs: 1116, 1117 (malware events) and 5001(real-time protection disabled).
Under Advanced Options, we include the Event IDs that we want to track:
Add Integration to existing host, Select the Agent Policy used earlier, save and continue
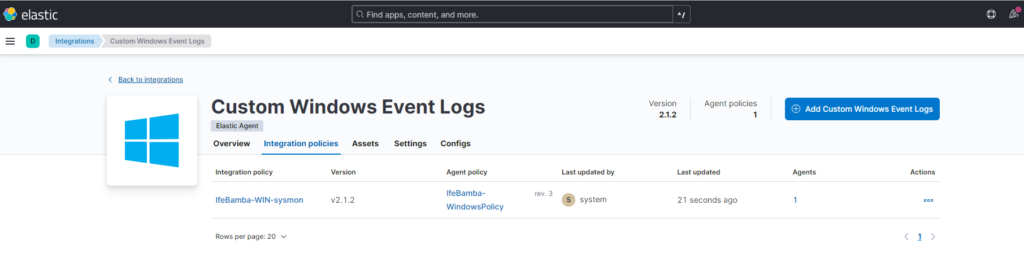
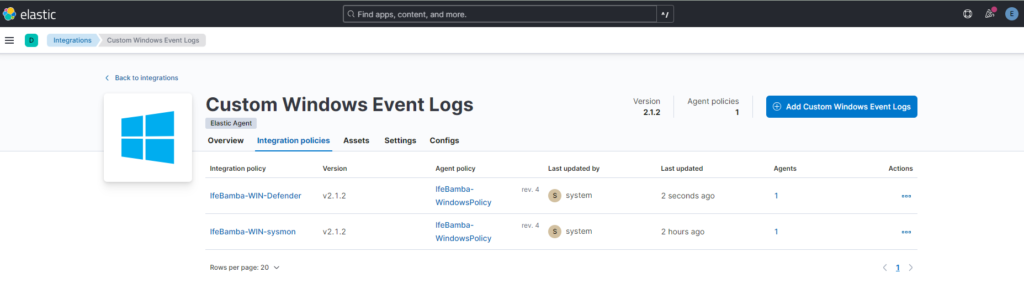
Screenshot showing the Windows Event logs added to Elasticsearch : Sysmon and Windows Defender Logs
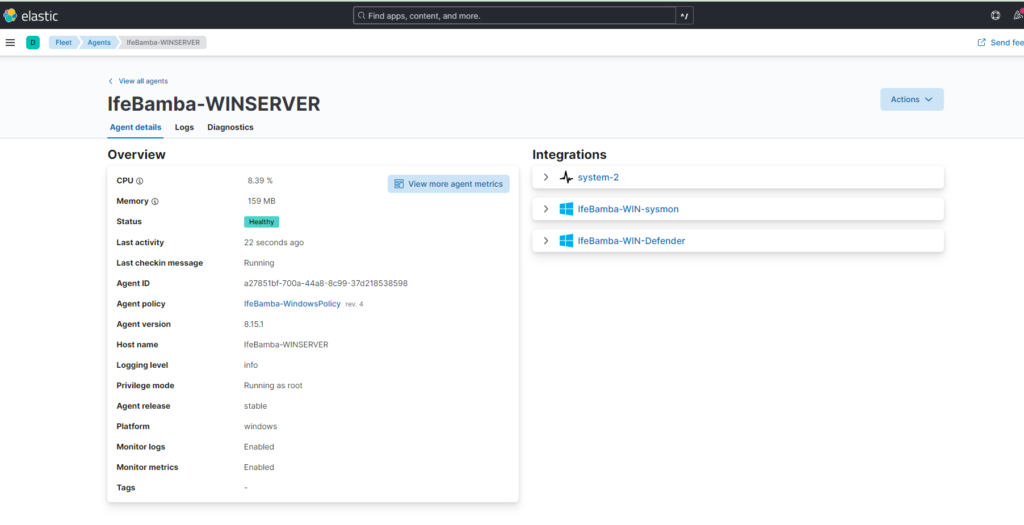
Elastic Agent winserver details: Seeing the CPU details and Memory usage shows that our Agent can communicate with our ElasticSearch Instance.
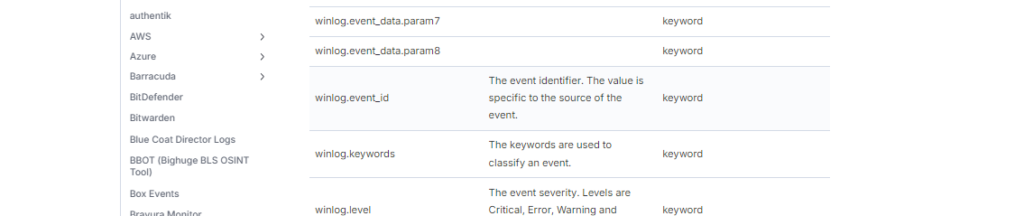
To view Custom Windows Event Logs, we can check the page in Elasticsearch documentation:
Custom Windows Event Logs | Documentation (elastic.co). Here, we are interested in the “winlog.event_id” Field Mapping:
To filter our ElasticSearch logs,
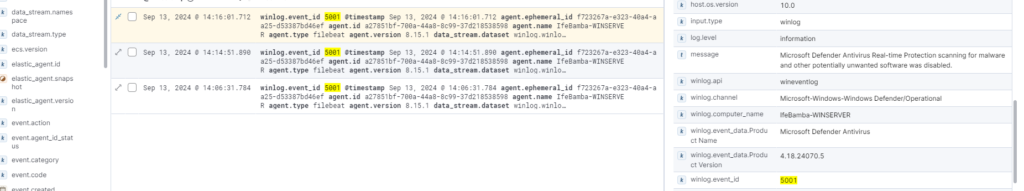
Elasticsearch > Analytics > Discover > Search “winlog.event_id” using ID 5001
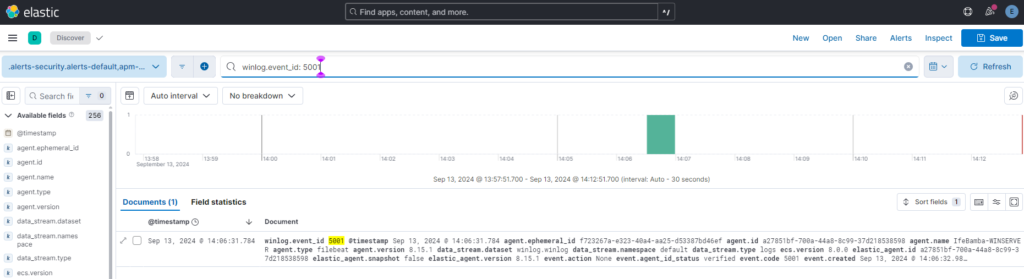
To trigger this event ID in Windows, we had to visit the Windows Server > Windows Security > Windows Defender > Disable Real time Protection as seen below: This event simulates a malware attack that disables windows Defender and triggers the 5001 Event ID.

Windows Defender Log Event as seen in ElasticSearch:

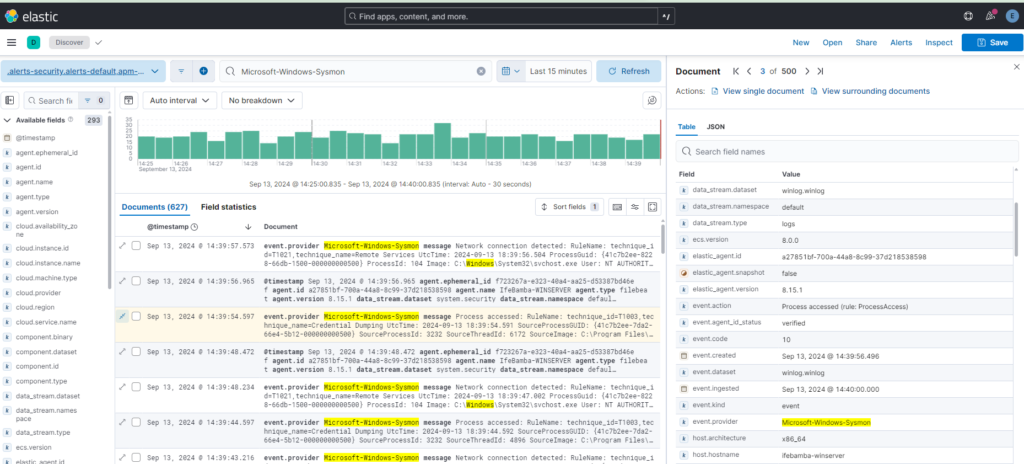
Sysmon Log Event as seen in ElasticSearch: